SoftEther VPN

SoftEther VPN - the academic project of Japanese university (University of Tsukuba), extended under licence GPLv2. Its main feature is support of the several VPN-reports compatible to original clients. It allows instead of park of servers from proprietary and open source decisions to use for connection of the clients working under control of different OS, one application. And simply to choose the necessary report depending on a concrete situation.
Are supported: SSL-VPN (HTTPS), IPsec, L2TP, MS-SSTP, L2TPv3, EtherIP and OpenVPN. SoftEther VPN works in modes remote-access and site-to-site, at levels L2 (Ethernet-bridging) and L3 (IP). In case of replacement OpenVPN we receive more simple configuration. There is a generator of ovpn-files for fast connection of the VPN-client.
Replacement SSTP VPN allows to refuse use of servers on the basis of Win2k8/2012, demanding the licence. Own report provides passage Ethernet atop HTTPS (from here and the project name - Software Ethernet), is characterised by good carrying capacity and low a latency. Its use gives the chance is transparent to connect some Ethernet-networks in one, that is necessity for additional decisions Ethernet-over-IP disappears.
The main thing - that it is compatible with NAT and works through standard 443rd port which usually is not blocked by fireproof walls of providers. This possibility allows to hide in general use VPN: from outside the traffic looks as usual and it is not found out by technologies Deep Packet Inspection. Actually, therefore it also became very popular in China where it use for detour of the Great Chinese firewall. Thus on client side virtual network adapter Ethernet, and on the server - the virtual switchboard is realised.
The big plus - presence NAT Traversal, included by default, that is it is not necessary to ask to open the administrator access to the VPN-server which is in an internal network. But there is more to come. In networks with fixed access at which are blocked all TCP - and UDP-packages (for example, public Wi-Fi), for creation VPN it is possible to use reports ICMP and DNS, usually not blocked by a fireproof wall. It is supported Dynamic DNS, allowing to get access at dynamically changing IP address.
Service VPN Gate named VPN Azure Cloud Service is for this purpose realised, - to it it is possible to organise connection from an internal network and then if necessary freely to get in a network. The client part contains the special plug-in VPN Gate, allowing to trace change IP and quickly to be connected to VPN Gate.
High performance and connection speed of 1 Gbytes/with without essential restrictions on volumes of the RAM and the minimum loading on the processor is provided. Therefore requirements to a server part are very low. Under tests SoftEther VPN bypasses on the same equipment original decisions. Enciphering AES-256 and RSA-4096, IPv4/IPv6, journalizing of the traffic and events is supported. Authentication of users local, RADIUS and domain Windows.
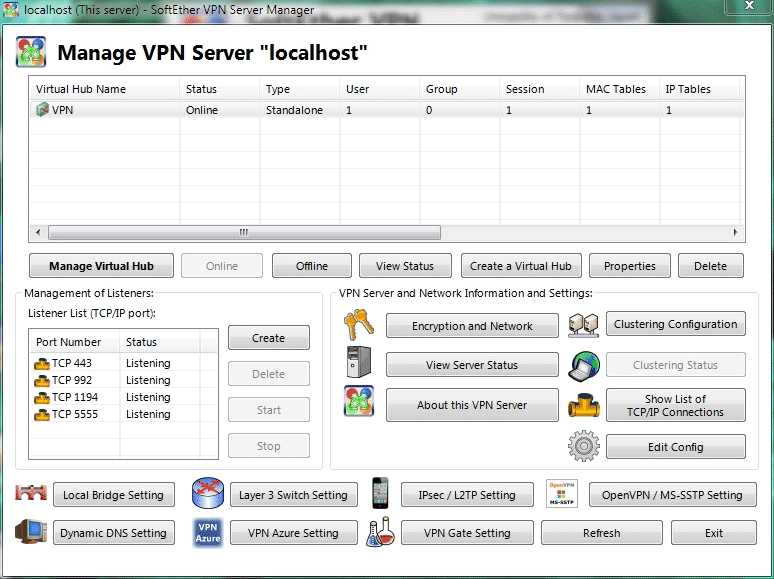
Administration of login accounts and safety parametres can be adjusted far off by means of graphic interface Server Manager (localisation only English, Japanese and Chinese) which is installed on Win - or the macOS-computer of the manager or by means of the utility of a command line vpncmd. Installation on Windows, Linux, macOS, FreeBSD and Solaris is possible. The source code and archive with the compiled application is accessible. For installation it is required to choose OS, a platform and a component (the server, the client, bridge …).
Linux-kernels 2.4/2.6/3.x are officially supported, but without problems works and in modern distribution kits with a kernel 4.х. In Linux it is enough to unpack archive and to start a file.instal.sh then time three to accept conditions of the licence and upon termination of to start the server.
Hardly in more details about server possibilities:
Set of virtual hubs. I.e. not each copy of the server serves only the clients, and all in a limit of one server.
Remote-Access (Client-to-LAN) and Site-to-Site (association of two and more LAN in one) tunnels.
Support L2TP/IPsec, OpenVPN, MS-SSTP, L2TPv3, EtherIP and the report
VPN through ICMP and through DNS (only through the report)
Dynamic DNS and NAT Traversal through free relays (yes-yes, it is possible to lift VPN the server with grey IP!)
Logging
Built in firewall
Support IPv6 in a L3-mode (well and in L2, of course, too)
Traffic shaping on groups of users or on concrete users
SecureNAT (user-space NAT and the DHCP-server). Conveniently on not-server Windows
Support VLAN
Support QoS with automatic a prioritization
Window of management of the server
Other VPN programs: